
Teacher pay crisis amid cuts: What it means for education
Teacher pay crisis amid cuts leads to urgent discussions on salary and support. Discover the impact on education and its future.
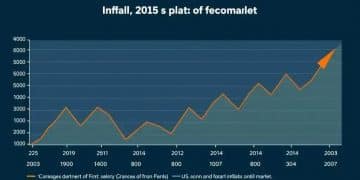
Inflation outlook: what to expect in US markets 2025
Inflation outlook indicates potential shifts in US markets by 2025. Learn how to prepare for changes ahead and adapt your investments.

Student loan oversight reductions: what you need to know
Student loan oversight reductions could impact your financial future. Explore the implications and changes on this crucial topic.

Private school choice surge US: what’s driving it?
Private school choice surge US is reshaping education landscapes. Discover key factors and impacts that are reshaping student success.

Snap eligibility changes 2025: what you need to know
Snap eligibility changes 2025 could impact many families. Learn how these adjustments might affect your benefits and assistance.

Naep reading decline high school us: what’s happening?
The NAEP reading decline in high school US raises concerns about educational standards and student outcomes. What are the underlying causes?





