IoT Vulnerabilities: 2026 Guide to Protecting US Smart Infrastructure

Protecting US smart infrastructure against emerging IoT vulnerabilities by 2026 requires a multi-layered approach encompassing proactive threat intelligence, robust security protocols, and continuous adaptive defence mechanisms.
The interconnected world of 2026 sees the United States increasingly reliant on smart infrastructure, from energy grids to transportation networks, all powered by the Internet of Things (IoT). However, this reliance brings with it a burgeoning landscape of cyber threats. Understanding and mitigating IoT smart infrastructure protection is not merely an IT concern; it is a matter of national security and economic stability. This comprehensive guide will delve into the critical vulnerabilities and offer practical, actionable solutions to fortify our essential systems against emerging attacks.
The Evolving Threat Landscape for IoT Infrastructure
The proliferation of IoT devices across US critical infrastructure has created an expansive attack surface that cyber adversaries are constantly probing. These threats are no longer theoretical; they represent tangible risks to public safety and operational continuity. The evolution of cyber warfare, coupled with the inherent vulnerabilities of many IoT devices, demands a sophisticated and adaptive defence strategy.
Attackers are becoming more resourceful, leveraging artificial intelligence and machine learning to identify and exploit weaknesses at an unprecedented pace. This necessitates a shift from reactive security measures to proactive threat hunting and predictive analytics. Understanding the motivations and capabilities of these advanced persistent threats (APTs) is the first step towards building resilient systems.
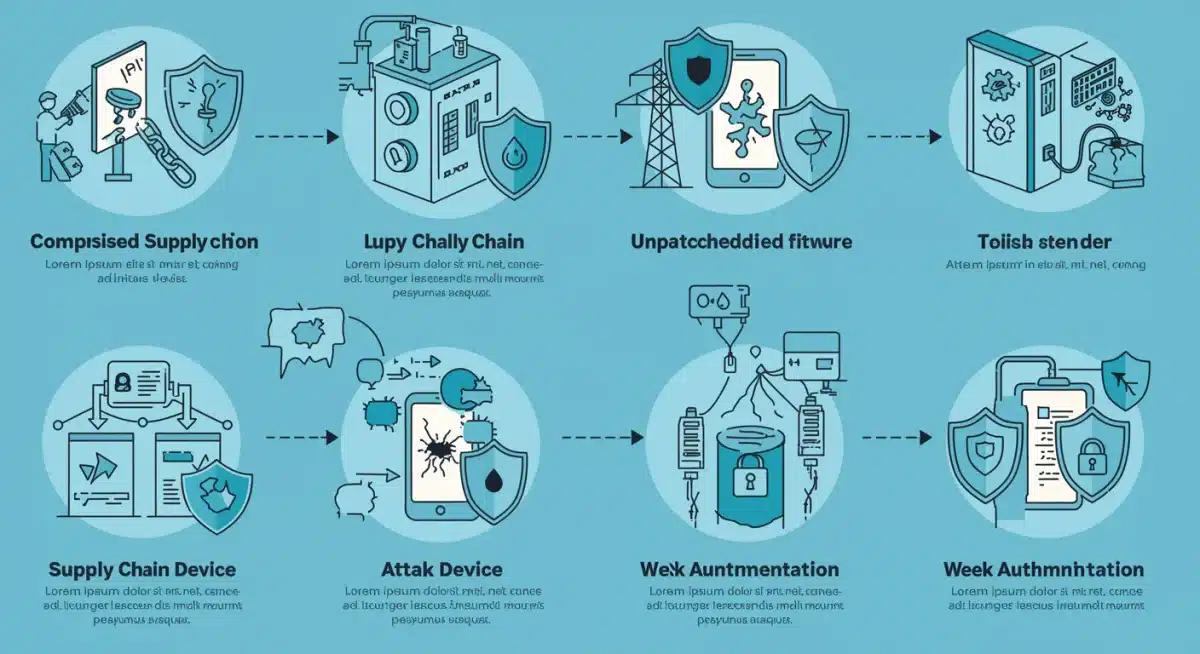
Common IoT Vulnerabilities Exploited in Critical Infrastructure
Several fundamental flaws continue to plague IoT devices, making them prime targets for malicious actors. Addressing these foundational issues is paramount for effective protection.
- Weak Authentication and Authorisation: Many IoT devices are deployed with default or easily guessable credentials, or lack robust access control mechanisms, providing an easy entry point for attackers.
- Insecure Network Services: Devices often expose unnecessary network services or use insecure communication protocols, creating avenues for remote exploitation and data interception.
- Lack of Secure Update Mechanisms: The absence of secure firmware update processes leaves devices vulnerable to compromise, as patches cannot be reliably or securely deployed.
- Inadequate Privacy Protection: Data collected by IoT devices, especially in smart cities, can be highly sensitive. Poor privacy controls can lead to data breaches and misuse.
The interconnected nature of smart infrastructure means that a compromise in one seemingly minor component can have cascading effects across an entire system. This highlights the importance of a holistic security approach that considers every device and every connection point.
Strategic Frameworks for Enhanced IoT Security
To effectively counter the escalating threats, a robust and integrated strategic framework is indispensable. This involves not only technological solutions but also policy, governance, and human factors. A multi-layered defence strategy, often referred to as ‘defence in depth’, is crucial for protecting diverse IoT ecosystems.
Government agencies, private sector entities, and academic institutions must collaborate to develop and implement comprehensive security standards. These standards should address the entire lifecycle of IoT devices, from design and manufacturing to deployment and end-of-life management.
Implementing Zero Trust Architectures
A fundamental shift in security philosophy is the adoption of Zero Trust principles. This model operates on the assumption that no user, device, or application should be trusted by default, regardless of whether they are inside or outside the network perimeter. Every access request must be authenticated and authorised.
In practice, this means:
- Strict Identity Verification: All users and devices must be explicitly verified before being granted access to resources.
- Least Privilege Access: Users and devices are granted only the minimum access necessary to perform their functions.
- Continuous Monitoring: Network traffic and device behaviour are constantly monitored for anomalies and potential threats.
Zero Trust significantly reduces the attack surface and limits the lateral movement of adversaries once they gain initial access, making it a cornerstone of effective IoT smart infrastructure protection.
Advanced Threat Detection and Response Mechanisms
Even with the most robust preventative measures, some attacks will inevitably bypass initial defences. Therefore, sophisticated threat detection and rapid response capabilities are critical for minimising the impact of successful breaches. The speed at which threats are identified and neutralised is often the determining factor in limiting damage.
Leveraging artificial intelligence (AI) and machine learning (ML) in security operations centres (SOCs) allows for the analysis of vast amounts of data, identifying patterns and anomalies that human analysts might miss. This proactive detection capability is vital in the fast-paced world of cyber threats.
AI-Powered Anomaly Detection
AI algorithms can learn the normal behaviour of IoT devices and networks within smart infrastructure. Any deviation from these established baselines can trigger alerts, indicating a potential compromise. This includes unusual data flows, unauthorised access attempts, or changes in device configurations.
The benefits of AI-powered detection include:
- Reduced False Positives: Advanced algorithms can differentiate between genuine threats and benign system fluctuations, reducing alert fatigue for security teams.
- Faster Detection Times: AI can process and analyse data much faster than humans, enabling near real-time threat identification.
- Predictive Capabilities: By analysing historical data, AI can predict potential attack vectors and vulnerabilities, allowing for proactive mitigation.
Integrating these AI capabilities into existing security infrastructure enhances the overall resilience of US smart infrastructure against emerging IoT threats.
Securing the IoT Supply Chain and Device Lifecycle
A significant vulnerability in IoT ecosystems often lies in the supply chain. Devices may come with pre-existing weaknesses, or components can be compromised during manufacturing or transit. Ensuring the integrity of the entire device lifecycle, from design to disposal, is paramount for comprehensive security.
This requires rigorous vetting of vendors, transparent reporting of security features, and secure coding practices throughout the development process. The concept of ‘security by design’ must be embedded at every stage.
Establishing Secure Development and Deployment Practices
Manufacturers and operators of IoT devices within smart infrastructure must adhere to stringent security standards. This includes:
- Secure Boot Mechanisms: Ensuring that only authorised and untampered firmware can be loaded onto devices.
- Hardware Security Modules (HSMs): Integrating hardware-based security features to protect cryptographic keys and sensitive data.
- Regular Security Audits: Conducting independent security assessments and penetration tests throughout the device lifecycle to identify and remediate vulnerabilities.
Furthermore, robust patch management programmes are essential. Devices must be designed to receive and apply security updates securely and efficiently, ensuring that newly discovered vulnerabilities can be addressed promptly across the entire infrastructure.
Regulatory Compliance and International Collaboration
Cybersecurity is not just a technical challenge; it is also a regulatory and geopolitical one. Establishing clear regulatory frameworks and fostering international collaboration are crucial for creating a safer digital environment for smart infrastructure. Standards and compliance ensure a baseline level of security across diverse systems.
The US government, in conjunction with international partners, must lead efforts to develop harmonised cybersecurity policies that address the cross-border nature of cyber threats. Information sharing and joint threat intelligence initiatives are vital for staying ahead of adversaries.
Key Regulatory and Policy Initiatives
Several initiatives are underway to strengthen IoT security, but more concerted efforts are needed by 2026. These include:
- NIST Cybersecurity Framework: Providing a voluntary framework for organisations to manage and reduce cybersecurity risks.
- Cybersecurity and Infrastructure Security Agency (CISA): Leading the national effort to understand, manage, and reduce risk to critical infrastructure.
- IoT Cybersecurity Improvement Act of 2020: Mandating minimum security requirements for IoT devices procured by the federal government.
However, these efforts must be continuously updated and expanded to keep pace with the rapidly evolving threat landscape. Collaboration with international bodies like the EU Agency for Cybersecurity (ENISA) can also provide valuable insights and best practices.
Building a Cyber-Resilient Workforce and Culture
Ultimately, technology alone cannot provide complete security. The human element remains a critical factor in the defence against cyberattacks. A well-trained, cyber-aware workforce and a strong organisational security culture are indispensable for effective IoT smart infrastructure protection.
Investing in continuous education and training programmes for all personnel involved in the operation and maintenance of smart infrastructure is essential. This includes engineers, IT professionals, and even end-users who interact with IoT devices.
Cybersecurity Training and Awareness Programmes
Effective training should cover a range of topics, from basic cyber hygiene to advanced threat analysis. Key areas include:
- Phishing and Social Engineering Awareness: Educating employees about common tactics used by attackers to gain initial access.
- Secure Coding Practices: For developers, ensuring that security is considered from the outset of any new IoT application or system.
- Incident Response Training: Equipping teams with the skills and procedures to effectively respond to and recover from cyber incidents.
Fostering a culture where cybersecurity is everyone’s responsibility, and where reporting suspicious activities is encouraged, significantly strengthens an organisation’s overall security posture. Regular drills and simulations can also help prepare teams for real-world scenarios.
| Key Protection Area | Brief Description |
|---|---|
| Zero Trust Adoption | Never trust, always verify; essential for limiting lateral movement in IoT networks. |
| AI-Powered Detection | Utilising AI/ML for real-time anomaly detection and predictive threat analysis. |
| Supply Chain Security | Ensuring integrity of IoT devices from manufacturing to deployment and maintenance. |
| Workforce Training | Developing a cyber-aware culture through continuous education and incident response drills. |
Frequently Asked Questions about IoT Infrastructure Security
▼
The primary challenges include the vast number and diversity of IoT devices, their often-limited security features, the interconnectedness of systems creating cascading risks, and the rapid evolution of sophisticated cyber threats. Legacy systems also present integration difficulties.
▼
Zero Trust enhances protection by mandating strict verification for every access request, regardless of location. This prevents unauthorised access and limits the lateral movement of attackers within the network, significantly reducing the impact of a potential breach.
▼
Supply chain security is critical because vulnerabilities can be introduced at any stage, from component manufacturing to device assembly and software development. Compromised components or firmware can create backdoors, making devices inherently insecure before deployment.
▼
AI plays a crucial role by analysing massive datasets to identify anomalies and patterns indicative of attacks, far beyond human capabilities. It enables faster threat detection, reduces false positives, and can even predict potential attack vectors, bolstering proactive defence strategies.
▼
Individuals can contribute by practising good cyber hygiene, using strong, unique passwords for their personal IoT devices, keeping software updated, and being vigilant against phishing attempts. Reporting suspicious activities to relevant authorities also helps maintain overall security awareness.
Conclusion
The imperative to protect US smart infrastructure from escalating IoT vulnerabilities by 2026 is undeniable. It demands a holistic, multi-faceted approach that integrates advanced technological solutions, robust regulatory frameworks, and a deeply ingrained culture of cybersecurity. By embracing Zero Trust principles, leveraging AI for proactive threat detection, securing the entire IoT supply chain, and investing in continuous workforce training, the United States can build resilient and secure smart infrastructure capable of withstanding the complex cyber threats of the future. The journey towards comprehensive IoT smart infrastructure protection is ongoing, requiring constant vigilance, adaptation, and collaboration across all sectors to safeguard our digital future.