5G Network Vulnerabilities: Securing Your Devices and Data

5G network vulnerabilities pose significant risks to devices and data, demanding robust security measures to protect against emerging threats in the evolving wireless landscape.
The advent of 5G technology promises lightning-fast connectivity and transformative applications, but it also introduces a new frontier of security challenges. Understanding and mitigating 5G network vulnerabilities is crucial for both individuals and organizations to secure their devices and data from emerging threats in this new wireless landscape.
Understanding the 5G Landscape and Its Security Implications
5G networks offer a vast improvement in speed and capacity compared to their predecessors. However, this enhanced capability comes with inherent security risks that need careful consideration and proactive management.
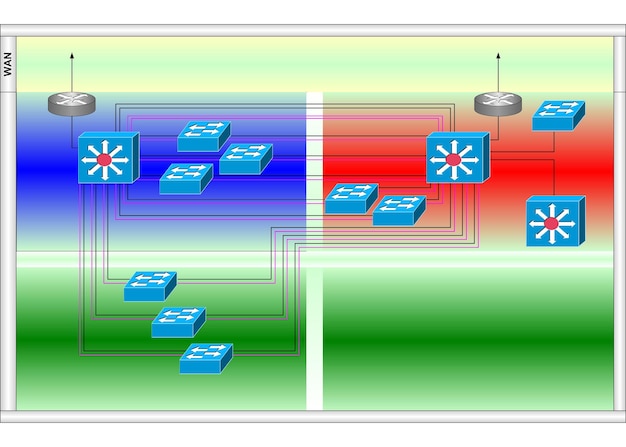
The increased complexity and expanded attack surface of 5G networks make them attractive targets for malicious actors. From data breaches to device manipulation, the potential consequences of these vulnerabilities are significant.
Key Differences Between 5G and Previous Generations
- Increased Bandwidth and Speed: Higher data transfer rates create broader avenues for data interception and manipulation.
- Network Slicing: While offering flexibility, network slicing introduces complexity that can lead to misconfigurations and vulnerabilities.
- Massive Device Connectivity: The sheer number of connected devices on 5G networks increases the attack surface, making it harder to monitor and secure all endpoints.
Emerging Security Challenges in 5G Networks
One of the primary concerns is the potential for vulnerabilities in the network infrastructure itself, including base stations and core network elements. This can lead to widespread service disruptions and data breaches.
Additionally, the increased reliance on software-defined networking (SDN) and network function virtualization (NFV) introduces new security concerns, as these technologies are susceptible to software bugs and exploits.
The complexity of the 5G ecosystem requires a comprehensive approach to security that addresses both network infrastructure and connected devices. Regular audits, penetration testing, and vulnerability assessments are essential to identify and mitigate potential risks.
Common 5G Network Vulnerabilities
Identifying common vulnerabilities is the first step in securing 5G networks. These weaknesses can be exploited by attackers to compromise devices, steal data, or disrupt services.
Understanding the specific types of vulnerabilities prevalent in 5G networks is crucial for developing effective security strategies. Let’s explore some of the most common:
Software Vulnerabilities
Software vulnerabilities are a significant concern in 5G networks due to their reliance on complex software systems. Bugs and flaws in software code can be exploited by attackers to gain unauthorized access or control.
Regular software updates and patching are essential to address these vulnerabilities promptly. However, the complexity of 5G networks can make it challenging to ensure that all systems are up-to-date.
Authentication and Authorization Weaknesses
Weaknesses in authentication and authorization mechanisms can allow attackers to impersonate legitimate users or devices. This can lead to unauthorized access to sensitive data and network resources.
Strong authentication methods, such as multi-factor authentication (MFA), are necessary to protect against these types of attacks. Additionally, proper authorization controls should be implemented to limit access based on the principle of least privilege.
Data Privacy Concerns
5G networks collect and process vast amounts of data, raising significant data privacy concerns. Vulnerabilities in data storage and transmission can expose sensitive information to unauthorized parties.
- Data Encryption: Encrypting data both in transit and at rest is crucial to protect against data breaches.
- Access Controls: Implementing strict access controls can limit who can access sensitive data.
- Data Minimization: Collecting only the data that is necessary for specific purposes can reduce the risk of data breaches.
These vulnerabilities can be exploited in various ways, including eavesdropping on communications, injecting malicious code into network traffic, and launching denial-of-service attacks. Therefore, robust security measures are essential to protect against these threats.
Securing Your Devices on 5G Networks
While network security is paramount, securing your devices is equally crucial. Devices represent the front line of defense against many 5G-related threats.
Taking proactive steps to protect your devices can significantly reduce the risk of compromise. Here are some essential security measures:
Keep Software Updated
Regularly updating your device’s operating system and applications is critical for patching security vulnerabilities. Software updates often include fixes for known flaws that attackers could exploit.
Enable automatic updates whenever possible to ensure that your devices are always running the latest security patches. This helps to minimize the window of opportunity for attackers.
Use Strong Passwords and Enable Multi-Factor Authentication
Using strong, unique passwords for all your accounts is essential for preventing unauthorized access. Avoid using easily guessable passwords or reusing the same password across multiple accounts.
Enable multi-factor authentication (MFA) whenever available to add an extra layer of security. MFA requires you to provide two or more verification factors, making it much harder for attackers to compromise your accounts.
Install a Reputable Antivirus or Mobile Security App
Antivirus and mobile security apps can help to detect and remove malware from your devices. These apps often include features such as real-time scanning, web protection, and anti-phishing capabilities.
Choose a reputable antivirus or mobile security app from a trusted vendor and keep it updated to ensure that it can effectively protect against the latest threats.

By implementing these security measures on your devices, you can significantly reduce your risk of becoming a victim of 5G-related cyberattacks. Staying vigilant and proactive is key.
Best Practices for Data Protection on 5G
Protecting data on 5G networks requires a multi-faceted approach that addresses various aspects of data security. Implementing best practices for data protection is essential for safeguarding sensitive information.
Here are some of the most effective strategies for ensuring data privacy and security on 5G networks:
Encryption
Encryption is a fundamental security control that protects data by converting it into an unreadable format. Encrypting data both in transit and at rest is crucial for preventing unauthorized access.
Use strong encryption algorithms and protocols to ensure that your data is effectively protected. Regularly review and update your encryption practices to stay ahead of evolving threats.
Access Control
Access control mechanisms restrict access to sensitive data based on predefined rules and policies. Implementing strong access controls can help to prevent unauthorized access and data breaches.
Follow the principle of least privilege, granting users only the minimum level of access required to perform their job functions. Regularly review and update access controls to ensure that they remain effective.
Data Loss Prevention (DLP)
Data loss prevention (DLP) solutions help to prevent sensitive data from leaving your organization’s control. DLP systems can monitor network traffic, email communications, and other data channels to identify and block unauthorized data transfers.
- Monitor Data: Continuously monitor data in use, in motion, and at rest to detect potential data breaches.
- Implement Policies: Define and enforce data loss prevention policies to prevent sensitive data from leaving your organization.
- Educate Users: Train users on data security best practices to prevent accidental data leaks.
By implementing these best practices for data protection, you can significantly reduce your risk of data breaches and other security incidents on 5G networks. Continuous monitoring and improvement are essential.
Future Trends in 5G Security
The future of 5G security will be shaped by emerging trends and technological advancements. Staying informed about these trends is crucial for proactively addressing future security challenges.
Here are some of the key trends that are likely to impact 5G security in the years to come:
Artificial Intelligence (AI) and Machine Learning (ML)
AI and ML technologies are increasingly being used to enhance security defenses. AI-powered security solutions can analyze network traffic, detect anomalies, and automate incident response.
These technologies can also be used to identify and mitigate zero-day vulnerabilities, providing a more proactive approach to security.
Quantum-Resistant Cryptography
Quantum computing poses a potential threat to current encryption algorithms. The development and deployment of quantum-resistant cryptography will be essential for securing 5G networks against future quantum attacks.
Researchers are actively working on developing new encryption algorithms that are resistant to quantum computing attacks. These algorithms will need to be implemented and deployed in 5G networks to ensure long-term security.
Zero Trust Security
The zero trust security model is based on the principle of “never trust, always verify.” This approach requires all users and devices to be authenticated and authorized before being granted access to network resources.
- Verify Identity: Continuously verify the identity of users and devices before granting access.
- Limit Access: Grant users only the minimum level of access required to perform their job functions.
- Monitor Activity: Continuously monitor network activity to detect and respond to potential threats.
Adopting a zero trust security model can significantly enhance the security of 5G networks by reducing the attack surface and limiting the impact of potential breaches. Continuous adaptation to emerging threats is key to success.
As 5G technology continues to evolve, it is essential to stay ahead of the curve and implement robust security measures to protect against emerging threats.
| Key Point | Brief Description |
|---|---|
| 🛡️ Software Updates | Regularly update software to patch security vulnerabilities. |
| 🔒 Strong Passwords | Use strong, unique passwords and enable multi-factor authentication. |
| 📡 Network Monitoring | Continuously monitor network activity for potential threats. |
| 🛡️ Data Encryption | Encrypt data to protect against unauthorized access. |
Frequently Asked Questions
▼
The main security risks include software vulnerabilities, authentication weaknesses, data privacy concerns, and increased attack surfaces due to massive device connectivity.
▼
Keep software updated, use strong passwords with MFA, install reputable antivirus apps, and be cautious about the apps you download and the permissions you grant.
▼
DLP is a set of techniques used to ensure users do not send sensitive or critical information outside the corporate network. It helps to prevent unauthorized sharing of confidential data.
▼
Quantum-resistant cryptography refers to cryptographic systems that are secure against attacks by quantum computers. It’s needed to protect data from future quantum computing threats.
▼
AI can analyze network traffic to detect anomalies, automate incident response, and proactively identify zero-day vulnerabilities, making security more adaptive and resilient.
Conclusion
Securing 5G networks and connected devices is a critical challenge that requires a comprehensive and proactive approach. By understanding the vulnerabilities, implementing best practices for data protection, and staying informed about emerging trends, individuals and organizations can mitigate the risks and leverage the benefits of 5G technology safely.