Cybersecurity Challenges US Infrastructure: Expert Predictions

Expert Insights: Predicting the Top 3 Cybersecurity Challenges for US Infrastructure in the Next 12 Months
In an increasingly interconnected world, the resilience of a nation’s critical infrastructure is paramount. The United States, with its vast and complex networks of energy, water, transportation, and communication systems, faces a dynamic and evolving threat landscape. Cybersecurity is no longer a niche concern for IT departments; it is a matter of national security, economic stability, and public safety. As we look ahead to the next 12 months, the challenges confronting US Infrastructure Cybersecurity are more complex and insidious than ever before. This article delves into insider knowledge and expert predictions, outlining the top three cybersecurity challenges that demand immediate and strategic attention.
The pace of digital transformation, while offering immense benefits, simultaneously expands the attack surface for malicious actors. From state-sponsored groups to sophisticated criminal syndicates, the motivation behind these attacks varies, but the potential for devastating consequences remains constant. Understanding these emerging threats is the first step towards building robust and adaptive defence mechanisms. Our analysis is based on consultations with leading cybersecurity experts, intelligence community reports, and observed global trends in cyber warfare and crime. The insights provided here are designed to equip decision-makers and cybersecurity professionals with the foresight needed to fortify their defences against the most pressing dangers.
The imperative to protect US Infrastructure Cybersecurity cannot be overstated. A successful attack on critical systems could lead to widespread power outages, contaminated water supplies, disruptions in financial markets, or even failures in emergency services. Such scenarios are not theoretical; they have been demonstrated in various forms around the world, underscoring the urgent need for proactive measures. By focusing on the most probable and impactful threats, we can allocate resources more effectively and develop targeted strategies that enhance the overall resilience of our nation’s vital assets.
Challenge 1: The Escalating Threat of Ransomware and Extortion on Operational Technology (OT) Systems
Perhaps the most immediate and pervasive threat to US Infrastructure Cybersecurity in the coming year is the relentless proliferation of ransomware and extortion attacks, particularly those targeting Operational Technology (OT) systems. Historically, ransomware primarily focused on IT networks, encrypting data and demanding payment for its release. However, attackers have increasingly shifted their sights to OT environments, which control physical processes in critical infrastructure sectors such as manufacturing, energy, and water treatment. The Colonial Pipeline attack in 2021 served as a stark reminder of the devastating impact such an attack can have, leading to fuel shortages and widespread disruption.
The reasons for this shift are clear: OT systems are often legacy systems, less regularly patched, and have unique protocols that make traditional IT security solutions less effective. Furthermore, the potential for physical disruption and safety risks associated with OT attacks creates immense pressure on victims to pay ransoms quickly. Attackers are exploiting this leverage, knowing that the cost of downtime and potential public safety hazards far outweighs the ransom demands for many critical infrastructure operators. The ‘double extortion’ tactic, where attackers not only encrypt data but also threaten to leak sensitive information, further exacerbates the pressure.
Experts predict that ransomware groups will continue to refine their tactics, moving beyond simple encryption to more sophisticated attacks that manipulate or damage OT processes directly. This could involve manipulating valves, changing pressure settings, or even causing physical damage to equipment, leading to catastrophic failures. The convergence of IT and OT networks, while offering efficiency gains, also creates new pathways for attackers to move laterally from less secure IT environments into critical OT systems. This blurring of lines demands a unified security strategy that addresses both domains comprehensively.
Another significant concern is the professionalisation of ransomware-as-a-service (RaaS) models. These models lower the barrier to entry for aspiring cybercriminals, providing them with sophisticated tools and infrastructure to launch attacks. This democratisation of cybercrime means that a wider array of actors, not just highly skilled state-sponsored groups, can pose a significant threat to US Infrastructure Cybersecurity. The global nature of these criminal enterprises also makes attribution and prosecution incredibly challenging, further empowering attackers.
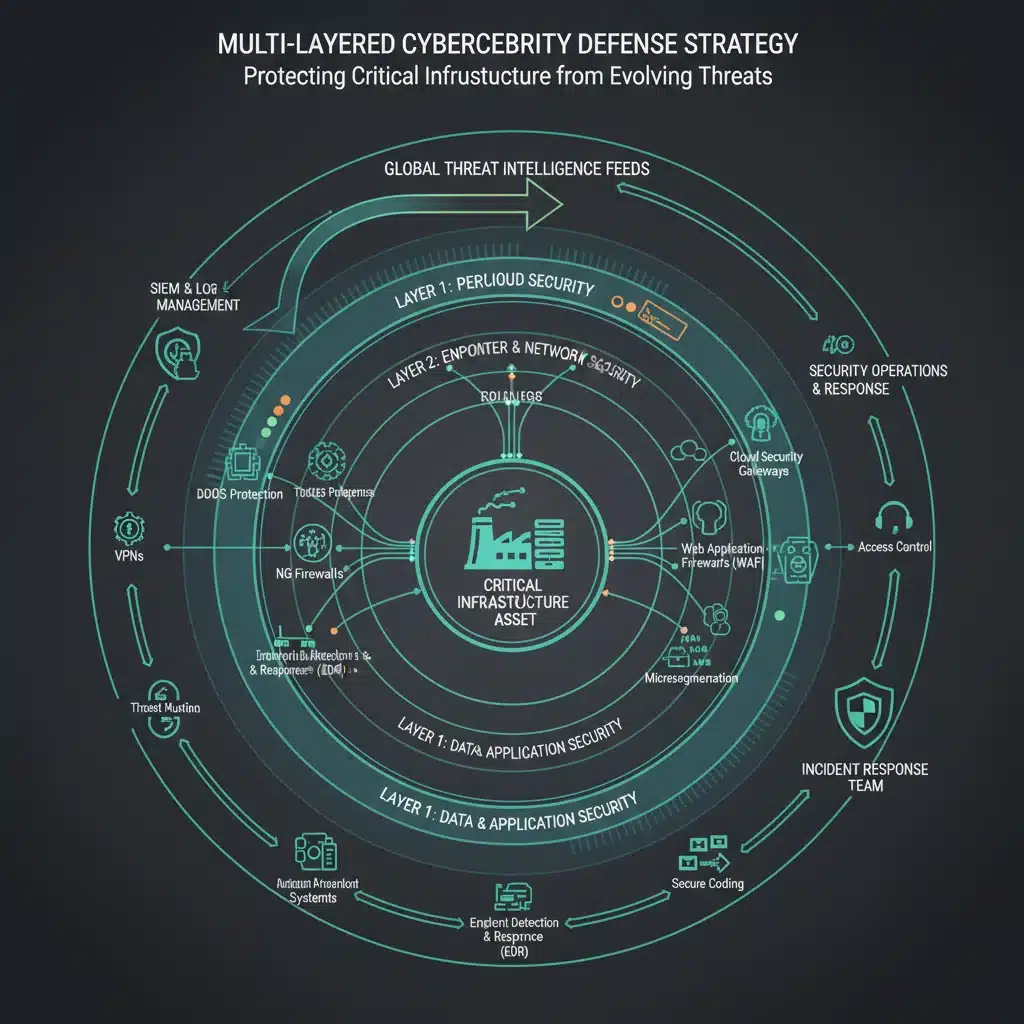
To counter this escalating threat, critical infrastructure organisations must prioritise segmenting IT and OT networks, implementing robust access controls, and developing comprehensive incident response plans specifically tailored for OT environments. Regular vulnerability assessments and penetration testing of OT systems are crucial, as is investing in specialised OT security solutions that can monitor and protect these unique environments. The focus must shift from simply recovering data to ensuring the continuity and integrity of physical operations, recognising that the stakes are higher than ever before.
Challenge 2: Supply Chain Vulnerabilities and Third-Party Risks
The interconnectedness of modern supply chains presents a significant Achilles’ heel for US Infrastructure Cybersecurity. A single vulnerability in a third-party vendor’s software or hardware can have a cascading effect, compromising numerous critical infrastructure entities that rely on that product or service. The SolarWinds attack in 2020 demonstrated the profound impact of such a supply chain compromise, where malicious code injected into a widely used network management software allowed attackers to infiltrate government agencies and private companies globally.
In the next 12 months, experts anticipate an intensification of attacks targeting the software supply chain. Attackers are increasingly looking for ways to compromise software at various stages of its development, from source code repositories to build pipelines and distribution channels. This ‘upstream’ compromise allows them to embed malicious code directly into legitimate software updates, which are then unwittingly installed by thousands of organisations, including critical infrastructure operators. The trust placed in software vendors becomes a formidable weapon for adversaries.
Beyond software, hardware supply chains also pose substantial risks. The introduction of counterfeit or tampered components into critical systems could create backdoors or introduce vulnerabilities that are extremely difficult to detect. As global manufacturing processes become more complex and distributed, ensuring the integrity of hardware components throughout the entire lifecycle is a monumental task. The reliance on a globalised supply chain, often involving components manufactured in adversarial nations, adds another layer of complexity and risk to US Infrastructure Cybersecurity.
The challenge extends beyond direct product compromises to the security posture of third-party service providers. Many critical infrastructure organisations outsource functions like managed IT services, cloud hosting, or maintenance. If these third-party providers have weak cybersecurity controls, they become attractive targets for attackers seeking to gain access to their clients’ networks. A breach at a smaller, less secure vendor can provide a gateway into larger, more resilient critical infrastructure systems.
Addressing supply chain vulnerabilities requires a multi-pronged approach. Critical infrastructure operators must implement rigorous vendor risk management programs, conducting thorough security assessments of all third-party providers and suppliers. This includes evaluating their cybersecurity policies, incident response capabilities, and adherence to industry best practices. Contracts should include clear cybersecurity requirements and clauses for audit rights.
Furthermore, organisations should adopt advanced security measures like software bill of materials (SBOMs) to gain transparency into the components and dependencies within their software. Employing secure development lifecycle (SDL) practices and robust code integrity checks can help mitigate risks during software creation. For hardware, establishing trusted supplier programs and implementing hardware security modules can offer enhanced protection. The goal is to build resilience into every link of the supply chain, understanding that the strength of the entire chain is determined by its weakest link.
Challenge 3: The Evolving Threat of Nation-State Sponsored Cyber Attacks and Advanced Persistent Threats (APTs)
While ransomware and supply chain attacks are significant, the most sophisticated and potentially catastrophic threats to US Infrastructure Cybersecurity stem from nation-state sponsored cyber attacks and Advanced Persistent Threats (APTs). These actors possess extensive resources, highly skilled personnel, and often long-term strategic objectives that go beyond financial gain, aiming for espionage, sabotage, or the disruption of critical services during geopolitical tensions.
Experts warn that state-sponsored groups will continue to engage in persistent reconnaissance and pre-positioning within critical infrastructure networks. This involves silently gaining access to systems, mapping network architectures, and implanting backdoors or other malicious tools that can be activated at a later date. This ‘living off the land’ approach, using legitimate system tools and processes, makes detection incredibly difficult. The objective is to establish a persistent presence that can be leveraged for intelligence gathering or to launch disruptive attacks when politically expedient.
The targets of these APTs are diverse, ranging from energy grids and water systems to telecommunications and financial infrastructure. The sophistication of their tools and techniques is constantly evolving, often leveraging zero-day vulnerabilities (unknown flaws in software) and highly customised malware that can bypass traditional security defences. Their ability to adapt and innovate means that defenders must also be equally agile and forward-thinking.
Geopolitical events are a significant driver for these types of attacks. In times of heightened international tension, the likelihood of nation-state actors targeting critical infrastructure increases dramatically. The aim could be to sow discord, exert political pressure, or prepare for potential kinetic conflicts by degrading an adversary’s capabilities. This makes the defence of US Infrastructure Cybersecurity a direct component of national defence and foreign policy.
Another emerging concern is the potential for nation-state actors to weaponise artificial intelligence (AI) and machine learning (ML) in their cyber operations. While still in nascent stages, the use of AI could enable attackers to automate reconnaissance, develop more effective phishing campaigns, or even autonomously identify and exploit vulnerabilities at unprecedented speeds. This would significantly shorten the detection and response window for defenders, creating a new arms race in the cyber domain.

Countering nation-state APTs demands a robust national cybersecurity strategy that integrates intelligence sharing, public-private partnerships, and continuous investment in advanced defensive capabilities. Critical infrastructure operators must adopt a ‘assume breach’ mindset, focusing not only on prevention but also on rapid detection, containment, and recovery. This includes implementing advanced threat detection systems, such as Security Information and Event Management (SIEM) and Extended Detection and Response (XDR) solutions, coupled with threat intelligence feeds that provide insights into nation-state tactics, techniques, and procedures (TTPs).
Furthermore, fostering a culture of cybersecurity awareness and training within organisations is paramount, as even the most sophisticated technologies can be bypassed by a successful social engineering attack. Regular red teaming exercises, simulating nation-state attacks, can help identify weaknesses and improve incident response capabilities. Collaboration with government agencies, such as CISA (Cybersecurity and Infrastructure Security Agency), is also vital for sharing threat intelligence and coordinating defensive efforts against these highly capable adversaries.
Beyond the Top 3: Other Pressing Concerns for US Infrastructure Cybersecurity
While the three challenges outlined above represent the most critical threats to US Infrastructure Cybersecurity in the coming 12 months, it is important to acknowledge other significant concerns that contribute to the overall risk landscape. These include the persistent shortage of skilled cybersecurity professionals, the challenges of securing legacy systems, and the rapid adoption of new technologies like the Internet of Things (IoT) and 5G.
The Cybersecurity Workforce Shortage
The demand for qualified cybersecurity professionals far outstrips the supply, creating a critical vulnerability across all sectors, especially within critical infrastructure. This talent gap means that many organisations struggle to implement and maintain robust security programmes, leaving them exposed to sophisticated threats. Addressing this requires long-term investment in education, training, and recruitment initiatives to build a diverse and skilled cybersecurity workforce capable of defending against evolving threats.
Securing Legacy Systems
Many critical infrastructure sectors rely on legacy systems that were not designed with modern cybersecurity threats in mind. These older systems are often difficult to patch, integrate with modern security tools, and may lack fundamental security features. Replacing them is often prohibitively expensive and disruptive. Therefore, organisations must develop strategies for securing these systems, which may include network segmentation, virtual patching, and continuous monitoring, to protect them from contemporary attacks.
The Rise of IoT and 5G
The proliferation of Internet of Things (IoT) devices in critical infrastructure for monitoring and control, coupled with the rollout of 5G networks, introduces new attack vectors. IoT devices are often deployed with weak security defaults, making them easy targets for compromise, which can then be used to gain access to broader networks. 5G networks, while offering significant speed and capacity, also expand the attack surface and introduce new complexities in securing network slices and edge computing environments. Proactive security-by-design principles are essential for these emerging technologies.
Developing a Resilient US Infrastructure Cybersecurity Posture
Successfully navigating the turbulent cybersecurity landscape of the next 12 months requires a multi-faceted and adaptive approach to US Infrastructure Cybersecurity. It’s not enough to simply react to threats; organisations must anticipate them and build resilience into their core operations. This involves a combination of technological solutions, robust processes, and a strong human element.
Firstly, fostering a culture of cybersecurity at all levels of an organisation is paramount. This means moving beyond technical controls to instill a security-first mindset among all employees, from the C-suite to frontline operators. Regular training, awareness campaigns, and clear communication about cyber risks are essential to empower individuals to be the first line of defence.
Secondly, continuous investment in cutting-edge cybersecurity technologies is non-negotiable. This includes advanced threat intelligence platforms, AI-driven anomaly detection systems, endpoint detection and response (EDR), and security orchestration, automation, and response (SOAR) solutions. These tools can help organisations detect and respond to threats more rapidly and efficiently, reducing the impact of successful attacks.
Thirdly, robust incident response and disaster recovery planning must be a top priority. Organisations must have well-defined, regularly tested plans for how to respond to a cyberattack, including communication protocols, forensic analysis procedures, and recovery strategies. The ability to quickly contain a breach and restore operations is crucial for minimising damage and maintaining public trust.
Finally, collaboration and information sharing are vital. The cybersecurity threat landscape is too vast and complex for any single entity to tackle alone. Public-private partnerships, industry-specific information sharing and analysis centres (ISACs), and international cooperation are essential for sharing threat intelligence, best practices, and lessons learned. This collective defence approach strengthens the overall resilience of US Infrastructure Cybersecurity against common adversaries.
Conclusion: A Call to Action for US Infrastructure Cybersecurity
The next 12 months will undoubtedly test the resilience of US Infrastructure Cybersecurity. The escalating threat of ransomware on OT systems, the pervasive vulnerabilities within supply chains, and the persistent, sophisticated attacks from nation-state actors represent a formidable trifecta of challenges. These threats are not merely technical; they have profound implications for national security, economic stability, and the daily lives of citizens.
The insights provided by experts underscore the urgent need for proactive, strategic, and collaborative action. Organisations operating critical infrastructure must move beyond compliance-driven security to adopt a risk-based approach that prioritises the most impactful threats. Investing in advanced security technologies, cultivating a strong cybersecurity culture, and fostering robust public-private partnerships are not just recommendations; they are imperatives for safeguarding our nation’s vital assets.
By understanding these top cybersecurity challenges and committing to a continuous improvement in defence strategies, the United States can enhance its resilience and ensure the continued operation of its critical infrastructure in the face of an ever-evolving cyber threat landscape. The time for decisive action in strengthening US Infrastructure Cybersecurity is now.





