Data Breach Response: A 72-Hour Plan for US Companies Following the Latest Regulatory Requirements (PRACTICAL SOLUTIONS, RECENT UPDATES)

In an increasingly interconnected digital landscape, the threat of a data breach is no longer a matter of ‘if’ but ‘when’. For US companies, the stakes are exceptionally high, with stringent regulatory requirements, significant financial penalties, and immense reputational damage hanging in the balance. The critical window for an effective response is often measured in hours, not days, with many regulations mandating notification within 72 hours of discovery. This comprehensive guide provides a practical, step-by-step 72-hour data breach response plan, meticulously crafted to align with the latest US regulatory requirements and equip your organisation with the tools and knowledge to navigate this challenging terrain.
Understanding the nuances of data breach response is paramount. It’s not merely about technical recovery; it’s about legal compliance, stakeholder communication, and long-term reputational management. A well-executed data breach response plan can significantly mitigate the impact of an incident, protect sensitive data, maintain customer trust, and ensure business continuity. Conversely, a haphazard or delayed response can exacerbate the crisis, leading to severe legal repercussions, irreparable brand damage, and substantial financial losses.
This article delves into the essential components of a robust data breach response, focusing on the immediate actions required within the crucial 72-hour timeframe. We will explore the evolving regulatory landscape in the US, highlighting key federal and state laws that mandate specific breach notification procedures. Furthermore, we will provide actionable insights and practical solutions for each stage of the response, from initial detection and containment to forensic analysis, legal counsel engagement, and stakeholder communication. Our aim is to empower US companies, irrespective of their size or industry, to develop and implement an effective data breach response plan that not only meets regulatory obligations but also fosters resilience and strengthens their overall cybersecurity posture.
The Accelerating Threat Landscape and Regulatory Imperatives
The volume and sophistication of cyberattacks continue to escalate, making data breaches an almost inevitable reality for businesses. From ransomware attacks that encrypt critical systems to phishing campaigns designed to steal credentials, the methods employed by malicious actors are constantly evolving. This dynamic threat landscape necessitates a proactive and agile approach to cybersecurity, with a particular emphasis on incident response planning.
Simultaneously, the regulatory environment surrounding data privacy and breach notification has become increasingly complex and stringent in the United States. Federal laws such as the Health Insurance Portability and Accountability Act (HIPAA) for healthcare entities, the Gramm-Leach-Bliley Act (GLBA) for financial institutions, and the Children’s Online Privacy Protection Act (COPPA) impose specific breach notification requirements. Beyond federal mandates, a patchwork of state-specific data breach notification laws adds another layer of complexity. Notable examples include the California Consumer Privacy Act (CCPA) and its successor, the California Privacy Rights Act (CPRA), the New York SHIELD Act, and numerous other state statutes that define personal information, specify notification timelines, and outline remediation efforts.
The implication for US companies is clear: a one-size-fits-all approach to data breach response is no longer sufficient. Organisations must understand the specific regulatory obligations applicable to their industry, the types of data they handle, and the geographic locations of their customers. Failure to comply with these diverse regulations can result in substantial fines, legal challenges, and a significant blow to an organisation’s reputation. This underscores the critical need for a meticulously planned and regularly updated data breach response plan that accounts for the multifaceted legal and operational challenges posed by a data breach.
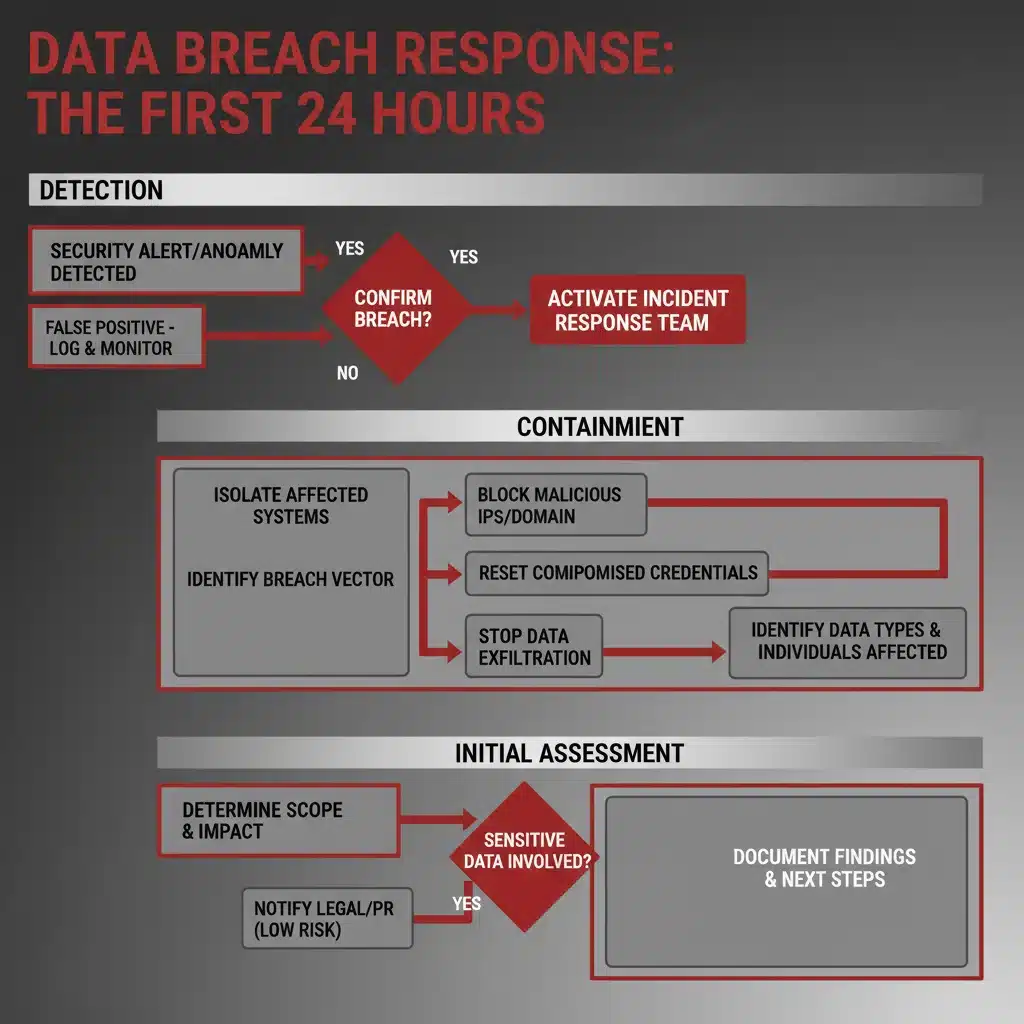
Phase 1: The Critical First 24 Hours – Detection, Containment, and Initial Assessment
The initial 24 hours following the discovery of a potential data breach are the most crucial. Swift and decisive action during this period can significantly limit the damage, reduce recovery time, and lay the groundwork for effective compliance and communication. This phase focuses on rapidly identifying the scope of the breach, isolating affected systems, and conducting an initial assessment of the incident.
Step 1: Activate the Incident Response Team (IRT)
Upon detection of a suspected data breach, the first immediate action is to activate your pre-defined Incident Response Team (IRT). This team should comprise individuals from various departments, including IT/security, legal, communications, human resources, and senior management. Each member should have clearly defined roles and responsibilities outlined in your incident response plan. The IRT’s immediate priorities are to establish a secure communication channel, document all actions taken, and initiate the formal incident response process.
Practical Solutions:
- Pre-defined Call Tree: Ensure an up-to-date call tree or communication protocol for immediate IRT activation.
- Secure Communication: Utilise out-of-band communication channels (e.g., encrypted messaging apps, dedicated phone lines) to prevent further compromise.
- Incident Response Platform: Implement an incident response platform or ticketing system to centralise documentation and task management.
Step 2: Containment and Isolation
The primary technical objective in the first hours is to contain the breach and prevent further unauthorised access or data exfiltration. This involves isolating affected systems, networks, or segments while minimising disruption to unaffected business operations. The goal is to stop the bleeding without destroying crucial forensic evidence.
Practical Solutions:
- Network Segmentation: Isolate compromised systems or network segments from the rest of the infrastructure.
- Credential Revocation: Immediately revoke or reset compromised user accounts, especially administrative credentials.
- Firewall Rules: Implement temporary firewall rules to block suspicious IP addresses or traffic patterns.
- Endpoint Disconnection: Disconnect affected endpoints (laptops, servers) from the network if necessary, after collecting volatile data.
Step 3: Initial Assessment and Evidence Preservation
While containment is underway, the IRT must begin an initial assessment to understand the nature, scope, and potential impact of the breach. This involves identifying the entry point, the type of data compromised, and the duration of the unauthorised access. Crucially, all actions must be taken with an eye towards preserving forensic evidence for later analysis and potential legal proceedings.
Practical Solutions:
- Log Collection: Secure and backup all relevant logs (firewall, intrusion detection/prevention systems, server, application, authentication logs).
- System Snapshots: Take forensic images or snapshots of compromised systems before making significant changes.
- Affected Data Identification: Begin identifying the specific types of data that may have been accessed or exfiltrated (e.g., PII, PHI, financial data, intellectual property).
- Timeline Reconstruction: Start building a preliminary timeline of the incident.
Phase 2: Hours 25-48 – In-depth Analysis, Legal Counsel, and Preliminary Notification Strategy
Once the initial containment and assessment are complete, the focus shifts to a more in-depth analysis of the incident, engaging legal counsel, and developing a preliminary notification strategy. This phase is critical for understanding the full extent of the breach and preparing for the mandatory reporting requirements.
Step 4: Comprehensive Forensic Analysis
A thorough forensic investigation is essential to understand how the breach occurred, what data was accessed or exfiltrated, and who was responsible. This often requires specialised expertise and tools to analyse logs, network traffic, and system artefacts. The findings of this analysis will directly inform your legal and communication strategies.
Practical Solutions:
- Engage Forensic Experts: If internal capabilities are limited, contract with third-party cybersecurity forensic firms.
- Root Cause Analysis: Determine the initial vector of compromise (e.g., phishing, unpatched vulnerability, misconfigured system).
- Data Exfiltration Confirmation: Verify if data was actually exfiltrated and identify the specific data sets involved.
- Impact Assessment: Quantify the potential impact on individuals, business operations, and financial standing.
Step 5: Engage Legal Counsel
Engaging legal counsel immediately is not just a best practice; it’s a critical step in managing the legal ramifications of a data breach. Attorneys specializing in cybersecurity and data privacy can guide the IRT through the complex web of federal and state notification laws, advise on potential liabilities, and help preserve attorney-client privilege over sensitive investigation details.
Practical Solutions:
- Pre-established Legal Retainer: Have a legal firm specialising in data privacy on retainer or identified in advance.
- Privilege Protection: Ensure all communications related to the breach investigation are conducted under the guidance of legal counsel to protect attorney-client privilege.
- Regulatory Interpretation: Obtain legal advice on specific notification requirements based on the type of data compromised and the affected individuals’ locations.
Step 6: Develop Preliminary Notification Strategy and Draft Communications
Within the 72-hour window, you must begin to formulate your notification strategy. This involves identifying who needs to be notified (regulators, affected individuals, business partners), what information needs to be conveyed, and through which channels. Even if the full scope is not yet known, drafting preliminary communications is crucial.
Practical Solutions:
- Identify Affected Parties: Determine the categories of individuals whose data was compromised and their geographical locations.
- Review Regulatory Requirements: Consult with legal counsel to understand specific notification timelines and content requirements for each applicable law (e.g., HIPAA, CCPA, state breach notification laws).
- Draft Notification Templates: Prepare draft notification letters for individuals, regulatory bodies, and potentially business partners.
- Public Relations Strategy: Begin planning your external communications strategy, including potential press releases or public statements.
Phase 3: Hours 49-72 – Regulatory Notification, Stakeholder Communication, and Remediation Planning
The final hours of the 72-hour window are dedicated to executing regulatory notifications, communicating with key stakeholders, and initiating long-term remediation efforts. This phase requires meticulous attention to detail and adherence to legal deadlines.
Step 7: Execute Regulatory Notifications
Many US federal and state laws mandate notification to regulatory bodies within 72 hours of discovering a data breach, especially if the breach poses a significant risk to affected individuals. This step is non-negotiable and requires precise execution based on the legal advice received.
Practical Solutions:
- Timely Submission: Ensure all required regulatory notifications are submitted within the mandated timeframe.
- Accurate Information: Provide accurate and complete information to regulators, even if preliminary, and follow up with updates as more details emerge.
- Document Everything: Keep detailed records of all notifications sent, including dates, times, and recipients.
Step 8: Communicate with Affected Individuals (as required)
While some regulations allow for a slightly longer timeframe for individual notifications, preparing and initiating this communication within 72 hours is often prudent, particularly for severe breaches. The content of these notifications must be clear, transparent, and actionable, advising individuals on steps they can take to protect themselves.
Practical Solutions:
- Clear and Concise Language: Avoid jargon; explain the breach in plain language.
- Actionable Advice: Provide specific steps individuals can take, such as monitoring credit reports, changing passwords, or enrolling in identity theft protection services.
- Offer Support: Provide contact information for a dedicated support line or email address for individuals with questions.
- Identity Theft Protection: Offer credit monitoring or identity theft protection services where appropriate or legally required.
Step 9: Engage with Law Enforcement (if applicable)
For certain types of breaches, especially those involving criminal activity or national security implications, engaging with law enforcement agencies (e.g., FBI, Secret Service) is critical. This should be done in consultation with legal counsel.
Practical Solutions:
- Legal Guidance: Consult with legal counsel before contacting law enforcement to understand the implications.
- Cooperation: Cooperate fully with law enforcement investigations while balancing business needs and legal obligations.
Step 10: Initiate Remediation and Recovery Planning
Even as notifications are underway, the IRT must begin planning for long-term remediation and recovery. This involves not only fixing the immediate vulnerabilities that led to the breach but also implementing more robust security measures to prevent future incidents.
Practical Solutions:
- Vulnerability Patching: Immediately patch identified vulnerabilities and address misconfigurations.
- Security Enhancements: Implement stronger security controls (e.g., multi-factor authentication, advanced endpoint detection, improved intrusion prevention).
- System Hardening: Rebuild or reconfigure compromised systems from known good backups.
- Employee Training: Reinforce security awareness training for all employees, focusing on the lessons learned from the breach.
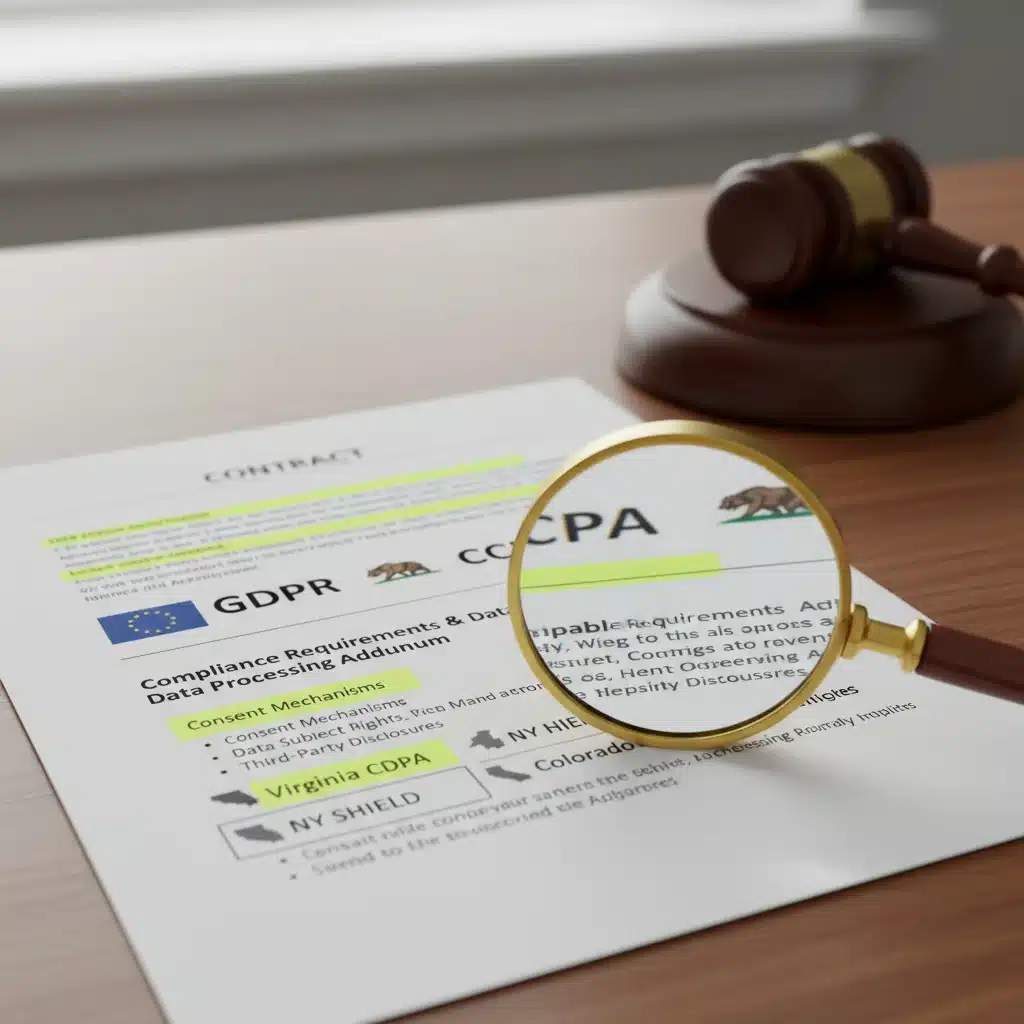
The Evolving US Regulatory Landscape: Key Considerations
The US regulatory environment for data breaches is a dynamic and fragmented one, requiring companies to stay abreast of both federal and state-specific mandates. While there isn’t a single overarching federal data breach law comparable to GDPR in Europe, various sector-specific federal laws and a myriad of state laws create a complex compliance challenge.
Federal Regulations:
- HIPAA (Health Insurance Portability and Accountability Act): Applies to healthcare providers, health plans, and healthcare clearinghouses. Mandates notification of breaches of unsecured protected health information (PHI) to affected individuals, the Secretary of Health and Human Services, and in some cases, the media. Notifications are generally required within 60 days, but investigations and initial assessments must begin immediately.
- GLBA (Gramm-Leach-Bliley Act): Applies to financial institutions. Requires them to explain their information-sharing practices to customers and to safeguard sensitive data. Breach notification typically falls under federal banking regulators’ guidelines and state laws.
- Children’s Online Privacy Protection Act (COPPA): Regulates online collection of personal information from children under 13. While not directly a breach notification law, a breach of COPPA-protected data would trigger other state notification laws and potentially FTC enforcement.
- NIST Cybersecurity Framework: While not a regulation, the National Institute of Standards and Technology (NIST) Cybersecurity Framework provides a voluntary set of guidelines for managing cybersecurity risks, including incident response, which is widely adopted and often referenced in compliance efforts for other regulations.
State-Specific Regulations:
Almost all US states have their own data breach notification laws, which vary significantly in their definitions of personal information, notification triggers, timelines, and required content. Some key examples include:
- California Consumer Privacy Act (CCPA) / California Privacy Rights Act (CPRA): Grants California consumers extensive rights over their personal information and includes specific breach notification requirements, particularly for breaches involving unencrypted or unredacted personal information. Failure to implement reasonable security procedures and practices can lead to statutory damages in the event of a breach.
- New York SHIELD Act (Stop Hacks and Improve Electronic Data Security Act): Broadened the definition of private information and expanded the scope of entities covered under New York’s breach notification law. It also requires companies to adopt reasonable safeguards to protect the security, confidentiality, and integrity of private information.
- Massachusetts Data Breach Law (M.G.L. c. 93H): One of the earliest and most stringent state laws, requiring businesses to implement a comprehensive written information security program (WISP) and providing specific notification rules.
- General State Breach Notification Laws: Most states require notification to affected residents and, in some cases, the state Attorney General or other regulatory bodies, typically within 30 to 90 days, but the investigation leading to these notifications must commence immediately.
Implications for US Companies:
- Jurisdictional Complexity: A single data breach can trigger notification obligations in multiple states, each with its own unique requirements. Companies must track the residency of affected individuals.
- Definition of Personal Information: The definition of ‘personal information’ varies by state, meaning what constitutes a reportable breach in one state might not in another.
- Risk of Harm: Many state laws include a ‘risk of harm’ threshold, meaning notification is only required if the breach poses a reasonable risk of harm to individuals. However, interpreting this threshold can be challenging and often requires legal counsel.
- Attorney General/Regulator Notification: In addition to individuals, many states require notification to the state Attorney General or other relevant state agencies.
- Credit Monitoring Offerings: Several states mandate offering free credit monitoring or identity theft protection for a specified period following certain types of breaches.
Given this intricate regulatory landscape, US companies must adopt a proactive and well-informed approach to data breach response. This includes maintaining up-to-date knowledge of all applicable federal and state laws, integrating these requirements into their incident response plans, and regularly reviewing their compliance strategies with legal experts.
Beyond 72 Hours: Long-Term Recovery and Resilience
While the 72-hour window is critical for immediate response and notification, a data breach incident does not conclude there. The post-breach period focuses on full recovery, continuous improvement, and building resilience against future attacks.
Phase 4: Post-Breach Analysis and Continuous Improvement
Once the immediate crisis has subsided, it’s essential to conduct a thorough post-mortem analysis of the incident. This involves reviewing the entire response process, identifying what worked well, and pinpointing areas for improvement. This analysis should lead to concrete changes in security policies, technologies, and incident response procedures.
Key Activities:
- Lessons Learned Meeting: Conduct a comprehensive review with the IRT and relevant stakeholders.
- Incident Report: Document the full incident, including the cause, impact, response actions, and lessons learned.
- Policy and Procedure Updates: Revise and update security policies, incident response plans, and employee training modules based on the findings.
- Technology Enhancements: Invest in new security technologies or upgrade existing ones to address identified vulnerabilities.
- Security Awareness Reinforcement: Conduct refresher training for employees on phishing, social engineering, and data handling best practices.
Phase 5: Building Long-Term Resilience
True resilience comes from embedding security into the organisational culture and continuously adapting to the evolving threat landscape. This involves ongoing risk assessments, regular security audits, and fostering a security-first mindset among all employees.
Key Activities:
- Regular Risk Assessments: Continuously assess and identify new threats and vulnerabilities.
- Penetration Testing and Vulnerability Scanning: Regularly test your systems for weaknesses.
- Tabletop Exercises: Conduct periodic tabletop exercises to simulate data breach scenarios and test the effectiveness of your incident response plan.
- Vendor Risk Management: Ensure third-party vendors and partners adhere to robust security standards, as they can often be a weak link.
- Data Minimisation and Encryption: Implement data minimisation practices (collect only what’s necessary) and robust encryption for sensitive data both at rest and in transit.
- Cyber Insurance Review: Regularly review and update your cyber insurance policy to ensure adequate coverage for potential breach costs.
Conclusion: Proactive Preparedness is the Best Defence
A data breach is a severe test for any organisation. For US companies, the intricate web of federal and state regulations, coupled with the ever-present threat of cyberattacks, makes a well-defined and regularly practiced data breach response plan an absolute necessity. The 72-hour window following discovery is not just a regulatory deadline; it’s a strategic opportunity to control the narrative, mitigate damage, and demonstrate commitment to data protection.
By following a structured approach that prioritises rapid detection, effective containment, thorough forensic analysis, expert legal counsel, and transparent communication, businesses can significantly improve their chances of navigating a data breach successfully. Remember, the goal is not just to comply with regulations but to protect your customers, preserve your reputation, and ensure the long-term viability of your business. Proactive preparedness, continuous improvement, and a culture of cybersecurity are the ultimate safeguards in today’s digital world. Invest in your data breach response plan today, because tomorrow might be too late.