Honeypots: Detect and Analyze Attacker Tactics in Your US Network

Honeypots are deception tools deployed within a US network to attract and analyze cyber attacks, providing valuable insights into attacker tactics and improving overall threat detection and response strategies.
In the realm of cybersecurity, understanding how attackers operate is crucial for effective defense. Honeypots: Deploying Deception Technology to Detect and Analyze Attacker Tactics in Your US Network offer a unique approach by luring potential threats into a controlled environment.
Understanding Honeypots: A Deception Strategy
Honeypots serve as decoys, designed to mimic valuable assets and attract cyber attackers. By carefully monitoring the interactions with these decoys, security professionals can gain deep insights into attacker methodologies, intentions, and potential vulnerabilities within the broader network.
What is a Honeypot?
A honeypot is a security resource whose value lies in being probed, attacked, or compromised. It’s a trap designed to attract malicious actors, allowing security teams to observe their behavior and gather intelligence.
Why Use Honeypots?
Deploying honeypots provides early warnings of attacks, gathers information about attackers, and can divert attackers from real assets. They offer a low false-positive rate because any interaction with a honeypot is inherently suspicious.

Honeypots are an excellent method to gain more insight on attacks on your US Networks. Key benefits include:
- Early Threat Detection: By attracting attacks, honeypots can provide early warnings of potential breaches.
- Attacker Profiling: They allow security teams to study attackers’ tools, techniques, and procedures (TTPs).
- Reduced False Positives: Interactions with honeypots are inherently suspicious, minimizing the risk of false alarms.
In conclusion, honeypots are a crucial component of a comprehensive threat detection strategy, providing actionable intelligence and enhanced security posture. This is especially important in keeping your US network protected.
Types of Honeypots and Their Applications
Honeypots come in various forms, each designed to emulate different systems and services. Choosing the right type depends on the specific goals and the environment in which they will be deployed. Understanding the different types is key to effective implementation.
Low-Interaction Honeypots
These honeypots mimic simple services or applications. They are easy to deploy but provide limited information about attacker behavior.
High-Interaction Honeypots
High-interaction honeypots simulate complex systems, giving attackers more freedom and providing more detailed information. However, they are more complex to manage and pose a higher risk.
The best type of honeypot will also depend on its design goal. Whether it’s a research honeypot, or production honeypot.
- Database Honeypots: Mimicking database servers to capture SQL injection attempts and other database-related attacks.
- Web Application Honeypots: Emulating web applications to detect vulnerabilities and identify web-based exploits.
- Client Honeypots: Actively searching for malicious servers or compromised websites, simulating user behavior to identify threats.
Ultimately, the type of honeypot deployed should align with the organization’s risk profile and security objectives. Understanding the nuances of each type is imperative for effective threat detection and analysis on US networks.
Deploying Honeypots in Your US Network: A Step-by-Step Guide
Deploying honeypots requires careful planning and execution. From selecting the right location to configuring monitoring tools, each step is critical to ensure effective threat detection and analysis. This guide offers a structured approach to deploying honeypots in your US network.
Assessing Your Network
Begin by understanding your network architecture and identifying critical assets. This will help determine the optimal location for your honeypots.
Choosing the Right Tools
Select honeypot software and monitoring tools that align with your security goals and technical capabilities. Consider open-source options like HoneyD or commercial solutions like TrapX.
To ensure your honeypots are a success you should consider:
- Network Segmentation: Place honeypots in segmented areas of the network to limit potential damage from attackers.
- Monitoring and Logging: Implement robust monitoring and logging to capture attacker activities and analyze their behavior.
- Regular Maintenance: Regularly update and maintain your honeypots to ensure they remain effective against evolving threats.
By following these steps, organizations can strategically deploy honeypots in their US networks to gain valuable insights into attacker tactics and improve their overall security posture.
Analyzing Attacker Tactics: Gathering Intelligence from Honeypots
The true value of honeypots lies in the intelligence they provide. By carefully analyzing attacker behavior, security teams can identify trends, understand motivations, and improve their defense mechanisms. The approach to analysis is crucial for deriving meaningful insights that help your US Network.
Identifying Attack Patterns
Look for common patterns in attacker behavior, such as the types of exploits used, the targets attacked, and the duration of the attack.
Understanding Attacker Motives
Determine whether the attacks are opportunistic or targeted. Understanding the attacker’s goals can help prioritize security efforts.
Utilzing the captured data from your honeypots can provide more insight that translates to better security for your enterprise.
- Log Analysis: Utilize log management tools to aggregate and analyze data from honeypots.
- Threat Intelligence Integration: Correlate honeypot data with external threat intelligence feeds to identify known attackers and attack campaigns.
- Incident Response Planning: Use honeypot data to refine incident response plans and improve reaction times.
Effective analysis of attacker tactics not only provides actionable intelligence but also enhances the organization’s ability to anticipate and prevent future attacks. By continuously learning from honeypot data, security teams can stay one step ahead of cyber threats in their US networks.
Best Practices for Maintaining Honeypots
Maintaining honeypots requires continuous effort and attention to detail. Regular updates, proper configuration, and ongoing monitoring are essential to ensure their effectiveness. Without the proper maintenance, your honeypots will not be as insightful as needed.
Keeping Software Up-to-Date
Regularly update honeypot software and operating systems to patch vulnerabilities and stay ahead of emerging threats.
Monitoring Logs and Alerts
Continuously monitor logs and alerts generated by honeypots to detect suspicious activity and respond promptly.
Here are some methods that will best keep your honeypots up to date and secure.
- Regular Audits: Conduct periodic audits to ensure honeypots are properly configured and functioning as expected.
- Security Assessments: Perform security assessments to identify and remediate any vulnerabilities in the honeypot environment.
- Staff Training: Provide ongoing training to security staff on how to manage and analyze honeypot data effectively.
By adhering to these best practices, organizations can maintain effective honeypots that provide valuable threat intelligence and enhance their overall security posture. Consistent upkeep is crucial for keeping US networks safe.
The Future of Honeypots: Trends and Innovations
The field of honeypots is constantly evolving to adapt to new threats and technologies. Emerging trends, such as AI-powered honeypots and cloud-based deployments, are shaping the future of deception technology. Let’s look at the growing innovations and trends.
AI-Powered Honeypots
AI is being used to create more realistic and adaptive honeypots that can mimic complex systems and behaviors, making them harder for attackers to detect.
Cloud-Based Honeypots
Cloud platforms offer scalability and flexibility for deploying and managing honeypots. They enable organizations to quickly set up and tear down honeypots as needed.
These advancements can help protect your US Network at any time and any scale.
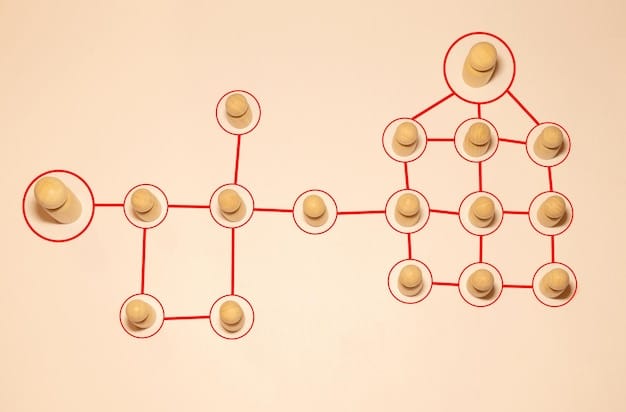
- Deception Grids: Advanced networks of interconnected honeypots that create a comprehensive deception environment.
- IoT Honeypots: Specialized honeypots designed to mimic IoT devices and capture attacks targeting the Internet of Things.
- Integration with SIEM: Seamless integration of honeypot data with Security Information and Event Management (SIEM) systems for centralized monitoring and analysis.
As cyber threats become more sophisticated, honeypots will continue to play a vital role in threat detection and intelligence gathering. Embracing these trends and innovations will help organizations stay ahead of attackers and protect their critical assets. The future is deception, and innovation is being developed to match.
| Key Point | Brief Description |
|---|---|
| 🎣What are Honeypots | Decoy systems to attract and study cyberattacks. |
| 🛡️Types of Honeypots | Low-interaction, high-interaction, database, and web app. |
| 🚨Analyzing Tactics | Identify patterns, motives, and integrate with Logs. |
| ☁️Future Trends | AI-powered, cloud-based, deception grids, IoT honeypots. |
FAQ
▼
The main goal of deploying honeypots is to attract and analyze cyberattacks, providing valuable intelligence on attacker tactics and improving overall network security. It gives your enterprise more insight into threats.
▼
Low-interaction honeypots mimic simple services or applications, offering an easier way to deploy and gather basic information about attacker behavior. These are better for smaller scale enterprises.
▼
Information gathered includes attack patterns, attacker motives, types of exploits used, and the targets being attacked, aiding in understanding potential vulnerabilities. This can help keep threats off of your US Network.
▼
Honeypots should be updated and maintained regularly to patch vulnerabilities, stay ahead of emerging threats, and ensure they effectively mimic real systems properly. You can never be too safe.
▼
Future trends shaping honeypot technology include AI-powered honeypots, cloud-based deployments, deception grids, IoT-specific honeypots, and enhanced integrations with SIEM systems for centralized threat analysis.
Conclusion
In conclusion, honeypots: Deploying Deception Technology to Detect and Analyze Attacker Tactics in Your US Network offers a proactive and insightful method for bolstering cyber defenses. By understanding the types, deployment strategies, and maintenance best practices, organizations can leverage honeypots to gather intelligence, improve incident response, and ultimately protect their valuable assets against evolving cyber threats.





