2026 Cyber Attack Landscape: US Ransomware Threats & Business Preparedness
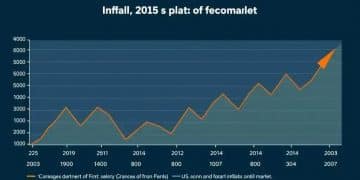
The digital frontier, while offering unprecedented opportunities for growth and innovation, simultaneously harbors an ever-growing array of sophisticated threats. As we cast our gaze towards 2026, the 2026 cyber landscape is shaping up to be more perilous than ever, particularly for US businesses. Recent analyses and expert forecasts paint a stark picture: a projected 15% increase in ransomware threats is not just a statistic but a clarion call for heightened vigilance and proactive defense strategies.
Ransomware, a particularly insidious form of cyber-attack, has evolved from a nuisance to a national security concern, capable of crippling critical infrastructure, disrupting supply chains, and inflicting severe financial and reputational damage. Its continued proliferation and increasing sophistication demand that businesses, regardless of size or sector, re-evaluate their cybersecurity postures and adapt to the evolving tactics of threat actors. This comprehensive guide will delve into the intricacies of the 2026 cyber landscape, unpack the drivers behind the surge in ransomware, and, most importantly, provide actionable insights and strategies for US businesses to fortify their defenses.
Understanding the Escalating Ransomware Threat in the 2026 Cyber Landscape
The 15% projected increase in ransomware attacks by 2026 is not an arbitrary figure; it’s a culmination of several intertwined factors that empower cybercriminals and make their illicit activities more profitable and scalable. To effectively combat this rise, US businesses must first comprehend the underlying dynamics.
The Evolution of Ransomware-as-a-Service (RaaS)
One of the primary drivers behind the escalating ransomware threat is the continued maturation of Ransomware-as-a-Service (RaaS) models. RaaS platforms lower the barrier to entry for aspiring cybercriminals, enabling individuals with limited technical expertise to launch sophisticated attacks. These services provide ready-made ransomware kits, infrastructure, and even technical support, operating on a subscription or profit-sharing basis. This democratisation of cybercrime means a larger pool of threat actors contributing to the burgeoning 2026 cyber landscape.
The Allure of Cryptocurrency and Untraceable Payments
The widespread adoption and relative anonymity of cryptocurrencies continue to be a significant enabler for ransomware operations. Bitcoin, Monero, and other digital currencies allow threat actors to receive ransom payments without easy traceability, making it challenging for law enforcement to track and apprehend perpetrators. This financial incentive fuels the ransomware ecosystem and encourages more frequent and aggressive attacks.
Exploiting Supply Chain Vulnerabilities
Cybercriminals are increasingly targeting supply chains, understanding that compromising a single vendor can provide access to multiple downstream organisations. This ‘one-to-many’ attack vector significantly amplifies the potential impact of a ransomware campaign. Businesses must recognise that their cybersecurity is only as strong as their weakest link in their supply chain, a critical consideration in the 2026 cyber landscape.
Sophisticated Social Engineering and Phishing Tactics
While technical vulnerabilities are often exploited, human error remains a primary gateway for ransomware. Phishing, spear-phishing, and other social engineering tactics are becoming increasingly sophisticated, leveraging AI-powered tools to craft highly convincing and personalised attacks. Employees, often the first line of defense, can inadvertently become the weakest link if not adequately trained and vigilant.
The Rise of Double Extortion and Data Exfiltration
Modern ransomware attacks often involve ‘double extortion’ tactics. Beyond encrypting data and demanding a ransom for its decryption, threat actors also exfiltrate sensitive data. If the victim refuses to pay, the attackers threaten to publish the stolen data on the dark web, adding another layer of pressure and increasing the potential for reputational damage, regulatory fines, and competitive disadvantage. This trend is a defining characteristic of the evolving 2026 cyber landscape.
Key Threats and Attack Vectors to Watch in the 2026 Cyber Landscape
Beyond ransomware, the 2026 cyber landscape will be characterised by a diverse array of threats, each demanding specific defensive measures. US businesses must be aware of these evolving attack vectors to build resilient cybersecurity strategies.
AI-Powered Cyber Attacks
The rapid advancements in artificial intelligence are a double-edged sword. While AI offers powerful tools for defense, it also empowers attackers. AI can be used to automate the creation of highly convincing phishing emails, develop more sophisticated malware, identify vulnerabilities at scale, and even automate attack execution. This will make detecting and defending against attacks significantly more challenging.
IoT and OT System Vulnerabilities
The proliferation of Internet of Things (IoT) devices and the convergence of IT and Operational Technology (OT) environments present growing attack surfaces. Many IoT devices often lack robust security features, making them easy targets for initial compromise. Attacks on OT systems, particularly in critical infrastructure sectors, can have devastating real-world consequences, from power outages to manufacturing disruptions. Securing these interconnected systems is paramount in the 2026 cyber landscape.
State-Sponsored Advanced Persistent Threats (APTs)
Nation-states continue to engage in sophisticated cyber espionage and sabotage, often targeting critical industries, research institutions, and government entities. These Advanced Persistent Threats (APTs) are characterised by their stealth, persistence, and significant resources, making them incredibly difficult to detect and mitigate. Businesses with valuable intellectual property or those operating in critical sectors are particularly at risk.
Deepfakes and Information Warfare
The rise of deepfake technology, capable of creating highly realistic but fabricated audio and video, poses a significant threat to corporate reputation and trust. Deepfakes can be used in social engineering attacks, to spread misinformation, manipulate stock prices, or damage executive credibility. Businesses must develop strategies to verify information and communicate transparently in an era of pervasive digital deception.
Cloud Environment Exploitation
As more businesses migrate their data and applications to the cloud, securing these environments becomes critical. Misconfigurations, identity and access management (IAM) vulnerabilities, and insecure APIs are common entry points for attackers targeting cloud infrastructure. A shared responsibility model for cloud security means businesses must rigorously uphold their end of the bargain.
Proactive Strategies for US Businesses in the 2026 Cyber Landscape
Given the intensified threat landscape, a reactive approach to cybersecurity is no longer sufficient. US businesses need to adopt a proactive, multi-layered defense strategy to protect their assets and ensure business continuity. Here are crucial steps to consider:
1. Implement a Robust Zero Trust Architecture
The traditional perimeter-based security model is increasingly obsolete. A Zero Trust architecture operates on the principle of ‘never trust, always verify.’ This means that no user or device, whether inside or outside the network, is granted access to resources without strict verification. Implementing Zero Trust involves strong authentication, micro-segmentation, and continuous monitoring of all access attempts and network traffic. This paradigm shift is essential for navigating the 2026 cyber landscape effectively.
2. Enhance Endpoint Detection and Response (EDR) and Extended Detection and Response (XDR)
Traditional antivirus solutions are often inadequate against sophisticated threats. EDR and XDR solutions provide advanced capabilities for detecting, investigating, and responding to threats across endpoints, networks, cloud environments, and applications. These platforms leverage AI and machine learning to identify anomalous behavior and rapidly contain threats before they can cause widespread damage.
3. Strengthen Identity and Access Management (IAM)
Compromised credentials remain a leading cause of breaches. Businesses must implement strong IAM practices, including multi-factor authentication (MFA) for all users and systems, regular review of access privileges (Principle of Least Privilege), and robust password policies. Privileged Access Management (PAM) solutions are critical for securing accounts with elevated permissions.
4. Priorise Employee Cybersecurity Training and Awareness
Your employees are your first line of defense. Regular, engaging, and up-to-date cybersecurity training is vital. This training should cover phishing recognition, password best practices, safe browsing habits, and how to report suspicious activities. Simulated phishing exercises can also help reinforce learning and identify areas for improvement. Human firewall strength is non-negotiable in the 2026 cyber landscape.
5. Develop and Regularly Test Incident Response Plans
Even with the best defenses, a breach is always a possibility. A well-defined and regularly tested incident response plan is crucial for minimising the impact of an attack. This plan should outline roles and responsibilities, communication protocols, containment strategies, recovery procedures, and post-incident analysis. Tabletop exercises and full-scale simulations can help identify gaps and ensure readiness.
6. Implement Robust Data Backup and Recovery Strategies
In the face of ransomware, having immutable, air-gapped, and regularly tested backups is paramount. Businesses must ensure that critical data is backed up off-site and offline, making it inaccessible to attackers. The ability to quickly restore data from clean backups can significantly reduce downtime and the likelihood of paying a ransom.
7. Conduct Regular Vulnerability Assessments and Penetration Testing
Proactively identifying and patching vulnerabilities is fundamental. Regular vulnerability assessments scan systems for known weaknesses, while penetration testing simulates real-world attacks to uncover exploitable flaws. These exercises provide invaluable insights into an organisation’s security posture and help prioritise remediation efforts.
8. Embrace Cyber Threat Intelligence
Staying informed about the latest threats, attack techniques, and adversary profiles is critical. Subscribing to threat intelligence feeds, participating in industry information-sharing groups, and leveraging security vendors’ insights can help businesses anticipate attacks and proactively adjust their defenses. Understanding the 2026 cyber landscape requires continuous learning.
9. Secure Your Supply Chain
Recognising the shared risk, businesses must extend their cybersecurity efforts to their third-party vendors and supply chain partners. This involves conducting due diligence, contractually mandating security requirements, and regularly auditing vendor security practices. Establishing a vendor risk management program is non-negotiable.
10. Consider Cyber Insurance
While not a substitute for robust cybersecurity, cyber insurance can provide a financial safety net in the event of a breach. It can help cover costs associated with incident response, legal fees, notification expenses, business interruption, and even ransom payments (though paying ransom is generally discouraged by law enforcement). Carefully review policy terms and understand what is covered.
Regulatory Landscape and Compliance in 2026
The 2026 cyber landscape will also be shaped by an evolving regulatory environment. US businesses operate under a patchwork of federal and state-level data privacy and cybersecurity regulations. Non-compliance can lead to significant fines, legal action, and reputational damage.
Key Regulations to Monitor:
- NIST Cybersecurity Framework: While voluntary, the National Institute of Standards and Technology (NIST) Cybersecurity Framework is widely adopted as a best practice guide for managing and reducing cyber risk. Adherence to this framework can significantly enhance an organisation’s security posture.
- CISA Directives: The Cybersecurity and Infrastructure Security Agency (CISA) plays a crucial role in protecting critical infrastructure. Businesses in these sectors must stay abreast of CISA’s directives and recommendations.
- State Data Privacy Laws: Laws like the California Consumer Privacy Act (CCPA) and its successor, the California Privacy Rights Act (CPRA), along with similar legislation emerging in other states, impose strict requirements on how businesses collect, process, and protect personal data.
- Sector-Specific Regulations: Industries such as healthcare (HIPAA), finance (GLBA, NYDFS Cybersecurity Regulation), and defense (CMMC) have their own stringent cybersecurity compliance requirements that will continue to evolve.
Businesses must conduct regular compliance audits and ensure their cybersecurity practices align with all applicable regulations. Legal counsel specialising in cybersecurity and data privacy should be consulted to navigate this complex landscape.
The Role of Government and Public-Private Partnerships
Addressing the challenges of the 2026 cyber landscape requires a collaborative effort between government agencies and the private sector. Initiatives aimed at intelligence sharing, capacity building, and coordinated response are vital.
Information Sharing and Analysis Centers (ISACs)
ISACs serve as central hubs for sharing critical cybersecurity threat information within specific sectors. Participation in relevant ISACs can provide businesses with timely intelligence, best practices, and a platform for collaboration with peers and government entities.
CISA’s Role in National Cyber Defense
CISA continues to be a cornerstone of national cyber defense, offering resources, guidance, and incident response support to both government and private sector organisations. Businesses should leverage CISA’s alerts, advisories, and services to enhance their resilience.
International Cooperation
Given the transnational nature of cybercrime, international cooperation among law enforcement agencies and governments is crucial for disrupting ransomware gangs, prosecuting cybercriminals, and establishing norms of responsible state behavior in cyberspace. While businesses primarily focus on their own defenses, they benefit immensely from these broader efforts to tame the wild west of the internet.
Preparing for Tomorrow: A Call to Action for US Businesses
The projected 15% increase in ransomware threats within the 2026 cyber landscape is not a reason for panic, but a powerful motivator for decisive action. Cybersecurity is no longer merely an IT department concern; it is a fundamental business risk that requires attention from the highest levels of management.
Boards of directors and senior leadership must champion a culture of cybersecurity, allocating adequate resources, empowering security teams, and integrating cyber risk management into overall business strategy. Investing in skilled cybersecurity professionals, advanced security technologies, and continuous training will yield significant returns in terms of resilience and business continuity.
The attackers are constantly innovating, and so must the defenders. By embracing a proactive, adaptive, and comprehensive cybersecurity strategy, US businesses can not only mitigate the risks posed by the evolving 2026 cyber landscape but also turn cybersecurity into a competitive advantage.
The time to prepare is now. As the digital world continues its relentless march forward, securing our digital assets and infrastructure will be the defining challenge for businesses in the years to come. Let the projected surge in ransomware be the impetus for transformation, ensuring that US businesses are not just surviving but thriving in the complex and challenging 2026 cyber landscape.